
FULL STACK IOT
from bare metal to orbital links

from bare metal to orbital links
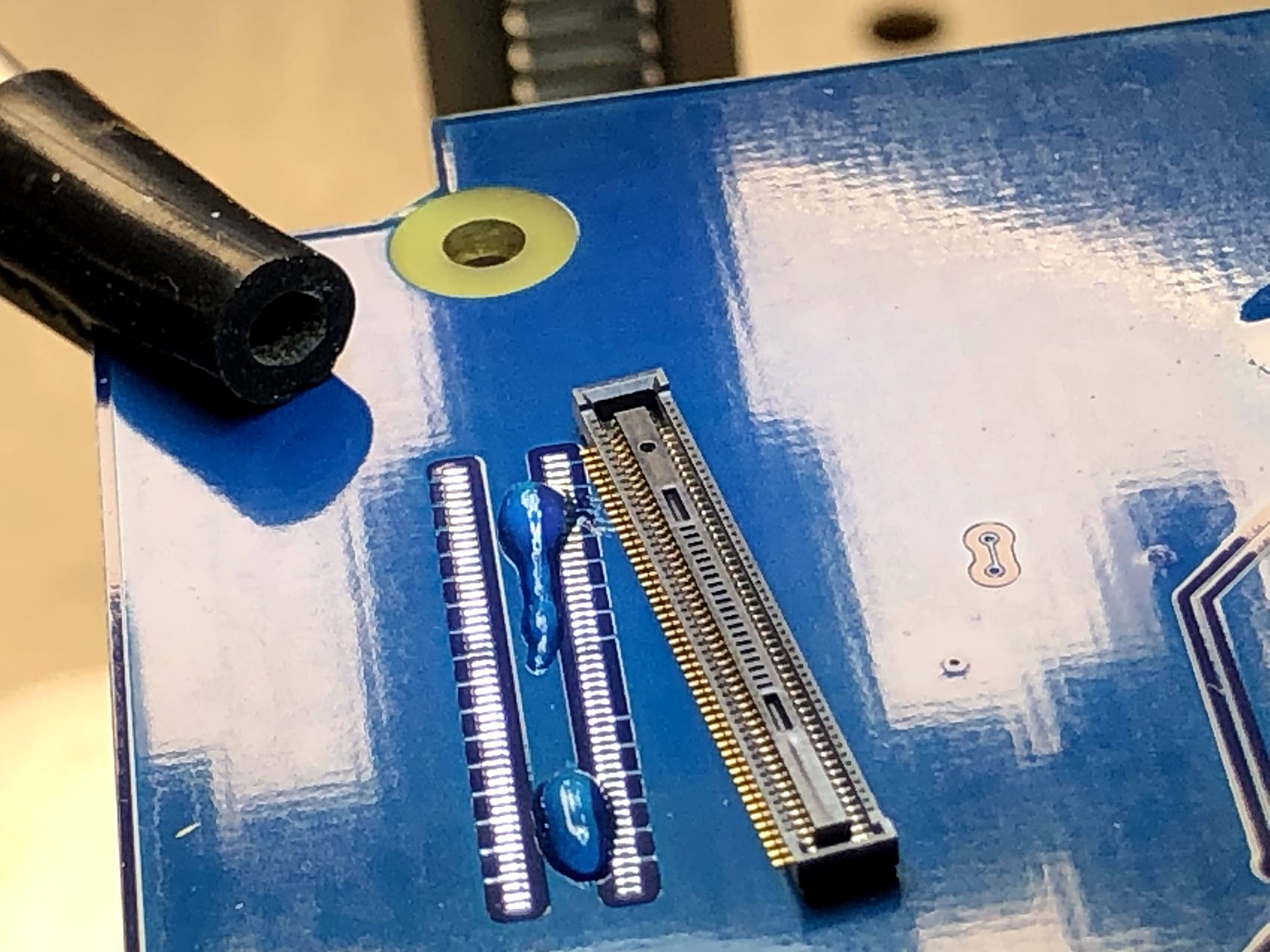
Where data begins. ARM Cortex silicon, hand-tuned firmware, and hardware designed to survive years on a coin cell in environments that destroy everything else.

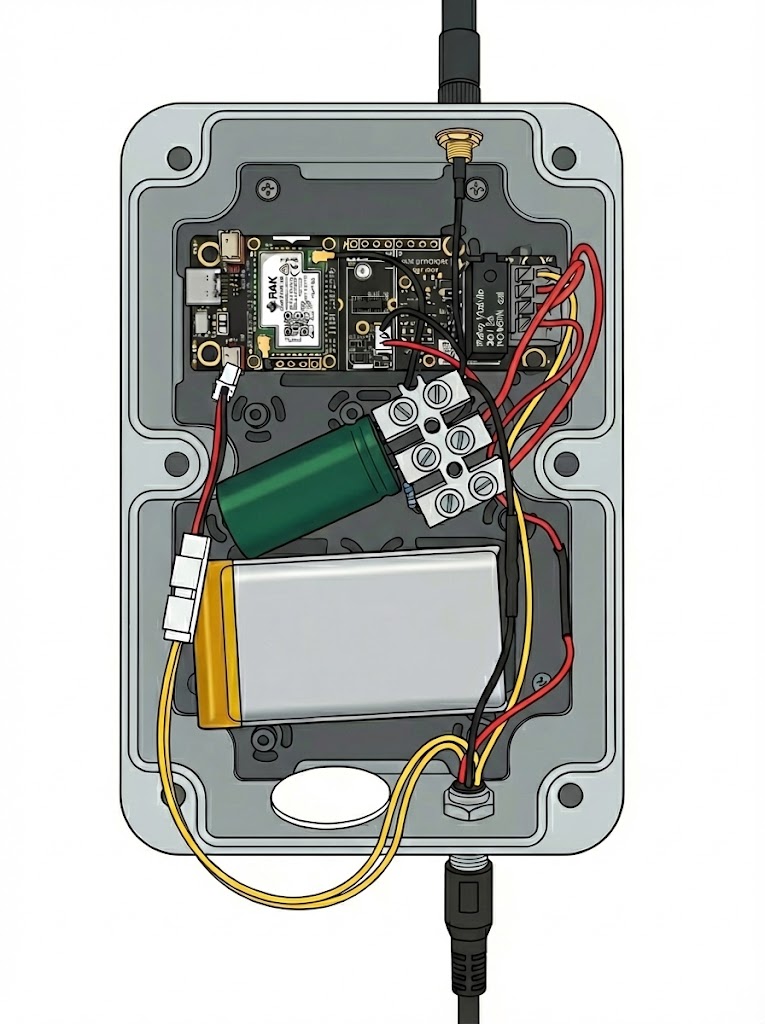



How data moves across terrain without infrastructure. LoRa chirp modulation, 20+ live mesh nodes, encrypted packets, GPS-tracked and battery-monitored in real time.
When terrestrial infrastructure doesn't exist. LEO satellite pass prediction, Doppler compensation, and store-and-forward scheduling that gets data out from anywhere on the planet.
Where edge telemetry becomes enterprise intelligence. MQTT brokers, device shadows, per-device policy authorization, and serverless pipelines that scale from 10 devices to 10 million.
Security isn't a feature — it's the architecture. X.509 device identity, private CA infrastructure, mutual TLS at every hop, and hardware roots of trust that can't be cloned.
If you need someone who architects IoT systems end-to-end —
not just configures platforms — let's talk.
What happens when a generalist engineer points the most capable AI models on the planet at real problems — for 73 days straight?
One engineer. Full-stack output. Infrastructure to IoT to frontend. I bring the AI compute, the context, and 14 years of building everything from circuit boards to cloud platforms.